A critical security vulnerability has been disclosed in the Java authentication library pac4j-jwt, used in applications implementing JWT-based authentication. The flaw, tracked as CVE-2026-29000, originates from improper validation logic in the JwtAuthenticator component when processing encrypted JWT tokens (JWE).
The issue allows an unauthenticated attacker to craft a malicious token and bypass signature verification. Because the library may incorrectly accept a JWE-wrapped PlainJWT, an attacker who knows the server’s RSA public key can forge a token with arbitrary claims and impersonate any user—including administrators.
This vulnerability directly impacts the authentication layer of affected applications and requires no prior privileges or user interaction. If exploited, attackers could gain unauthorized access to protected resources simply by presenting a specially crafted JWT.
The vulnerability affects the org.pac4j:pac4j-jwt package across multiple major versions of the pac4j framework.
Why This Matters
CVE-2026-29000 is critical because it allows attackers to completely bypass authentication and impersonate any user, including administrators, without knowing passwords, secrets, or tokens. Vulnerabilities like CVE-2026-29000 demonstrate how flaws in widely used authentication libraries can expose applications to account takeover and privilege escalation, making rapid dependency updates essential for maintaining application security.
Impact of Vulnerability
- Severity: CVE-2026-29000 is rated CRITICAL.
- Impact and Risk: An attacker can expose applications to account takeover and privilege escalation.
- Exploitation: Public proof-of-concept (PoC) exploits are reported and referenced online. PoC code availability has been disclosed by multiple security researchers and advisories, indicating that the vulnerability can be practically exploited, and this vulnerability is not theoretical.
- Affected Systems: CVE-2026-29000 affects the org.pac4j:pac4j-jwt across multiple major versions of the pac4j framework. The impact is at the identity and access layer, meaning any system relying on this library to validate encrypted JWTs is at risk.
- Attack Vector: Remote, unauthenticated.
Affected Versions
- pac4j-jwt < 4.5.9
- pac4j-jwt >= 5.0.0-RC1 and < 5.7.9
- pac4j-jwt >= 6.0.4.1 and < 6.3.3
Patched Versions
- 4.5.9
- 5.7.9
- 6.3.3
Recommended Actions
Upgrade immediately to a patched version (4.5.9, 5.7.9, or 6.3.3 or later) and review authentication logs for suspicious activity.
Learn More
Discover Where This Vulnerability Exists
HCL AppScan can scan open-source libraries to accurately identify usage and versions of the org.pac4j:pac4j-jwt library and flag all affected versions associated with CVE-2026-29000 across scanned codebases. Through these query capabilities, security teams can rapidly search and identify the precise scope of exposure.
With proactive monitoring, users are automatically informed when new vulnerabilities arise in any of their scanned projects, ensuring AppScan customers are promptly notified when a critical issue impacts previously assessed applications. Each finding includes detailed risk context, version-specific remediation guidance, and prioritization data, enabling teams to remediate authentication bypass vulnerabilities quickly and reduce the risk of unauthorized access or privilege escalation.
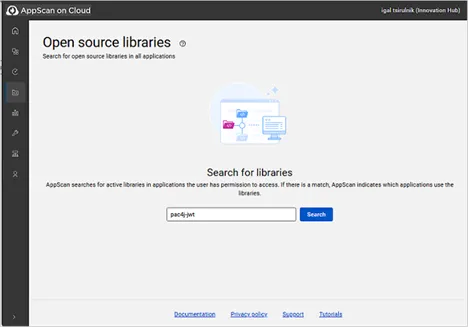
Figure 1 illustrates how to search for the pac4j-jwt vulnerability via HCL AppScan on Cloud.
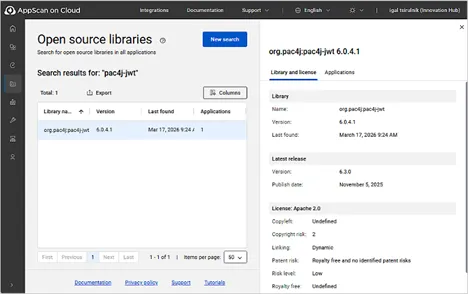
Figure 2 shows the open source library scan results, including library name and version number.
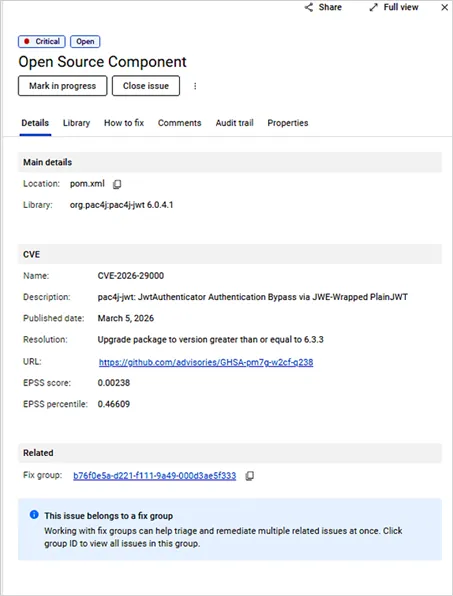
Figure 3 highlights the affected open source component, including version details and recommended remediation steps.
Take Action
Reduce your risk by running a scan now to quickly identify any applications affected by pac4j-jwt vulnerabilities. Once detected, remediate promptly by upgrading to a patched version to prevent authentication bypass and unauthorized access.
If you need assistance, our Customer Support Team is available to help guide you through detection and remediation steps.
Start a Conversation with Us
We’re here to help you find the right solutions and support you in achieving your business goals.



